Tech | 10/12/2022
After Tornado Cash – Why Privacy-Preserving Tools Shouldn’t Be Discredited Nor Banned
Key Takeaways: |
– On August 8th, the autonomous and Eth-based smart contract mixer Tornado Cash was sanctioned by the U.S. Treasury Office of Foreign Assets Control (OFAC). After this takedown, privacy has logically been at the center of Web3 debates. – While the platform has been sanctioned, we believe that Zero-Knowledge-Proof (ZKP) technologies used by Tornado Cash, including Linkable Ring Signatures, are key foundations for the future of privacy and should not be discredited nor banned. – Ledger has stood for privacy since the beginning, and will keep fighting for it. We believe that privacy is a human right, and that the future of Web3 must be built with privacy-enhancing tools as fundamental layers. |
Tornado Cash: A little bit of context
Tornado Cash is an autonomous cryptocurrency tumbler on the Ethereum blockchain based on zero-knowledge-proof (ZKP) technology allowing users to maintain privacy between deposit and withdrawal addresses.
Lot of people use it to hide their identity for many reasons (people caring about their privacy, living in dangerous countries, celebrities…). Since it can hide the source of Ethereum, unfortunately, there is also a money laundering use case, which is the reason why the US Treasury Department decided to sanction the cryptocurrency tumbler on August 8, 2022.
This article focuses on the fact that behind the U.S. sanction, Tornado Cash contains a key building block of the privacy-enhancing zero-knowledge-proof cryptography: the “linkable ring signatures”, a kind of signatures designed to enhance privacy for various applications. We believe such tools are essential for the future of privacy, and so their concrete use cases should be duly examined.
This tool used for the conception of the Tornado protocol finds many privacy-enhancing applications. Beyond confidential transactions, these range from anonymous airdrops to voting systems and proof/endorsement solutions. We will tackle all these use cases further down in this article.
How “Classic Signatures” Limit Your Privacy
In classic signature algorithms, a user signs a message using a secret key, which can be verified using its public key. Thus, the public key is a pseudonymization of the user’s identity.
The issue is that by tracing a public key, it is possible to check all related transactions using a blockchain explorer. It is therefore easy to trace a user given any additional metadata. In other words, these signatures do not respect your privacy.
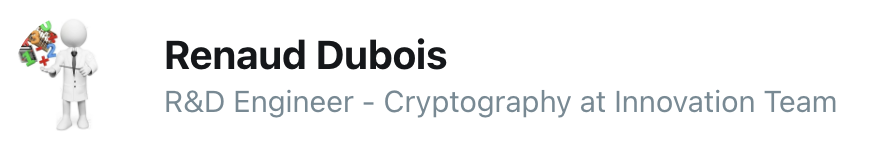
Here is what a basic signature looks like:
Classic signature
As the above drawing makes obvious, even though the signer used its private key and the third party has only access to the signature and public key, the third party will be able to trace from which address this public key was issued.
How “Ring Signatures” Enhance Your Privacy
In contrast to classic signatures, advanced signatures like ring and linkable signatures, such as the ones contained in Tornado Cash, provide increased anonymity features.
Ring signatures gather public keys of a ring (a subset) of users and enable a member to sign on behalf of the group with its unique secret key. The required anonymity property is that it is impossible for the verifier to identify from which member of the group the signature was issued.
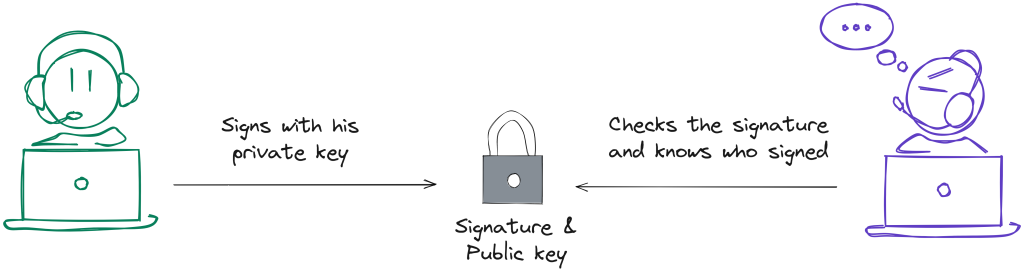
Here is what a ring signature looks like:
Ring signature
As you can see in the above example, even though only one member of the group (or “ring”) has signed with his private key, the third party who will check the signature won’t be able to know which member it was. However, he will have the certainty that the signature is legit and was issued by a real member of the group.
Little overview of the tech side
Here is what a simplified signatures API (we omit context, nonce, errors and hash for simplicity sake) looks like:
s_i=SIGNATURE( M, sk_i)
b=VERIFY( M, pk_i, s)
For a ring signature the API looks like:
s_i=RING_SIGNATURE( M, sk_i)
b=VERIFY(M, pk_1, pk_2, …, pk_n, s)
Where b is a boolean, s_i the signature of message M. n is the number of users of the ring, pk_i (resp. sk_i) the public (resp. secret) key of user i. Given s_i and s_i’, the verifier cannot distinguish the pseudonym i from i’.
The Linkable Property of “Ring Signatures”
The linkability property is an additional feature that enables an entity to identify if two signatures of the same message have been issued by the same user, without knowing the identity of that user.
This additional property is important to provide anonymity while maintaining double spend (for cryptocurrency usage) or double claim (for fidelity reward, voting system) infeasible.
Note that the linkability property can easily be activated/deactivated at system level by choosing to implement anti-replay description of message M.
Let’s take for instance the previous genuine check example. If it is convenient to implement linkability, then the genuine check message is designed to be unique per user. Otherwise, adding some timestamp provides a different value for genuine challenge c and disables likability.
A Wide Range of Privacy-Enhancing Use Cases
A simple example of Ring Signatures use case that we can imagine would be to replace a classical ECDSA by a RING_SIG in the genuine check of Ledger Live. Doing so, a privacy maximalist user is given the certainty that even Ledger Backend can’t learn anything more than the identity of the Ring from the endorsement procedure. There are applications in ZKP (Zero-Knowledge Proof) protocols and decentralized identifiers.
Another example of Linkable signatures use case could be an anonymous airdrop. Let’s say a manufacturer uses a linkable ring signature for its genuine check, and decides to provide its users with an airdrop (such as an ENS).
The issue is that:
- The manufacturer doesn’t want to let a single user claim many ENS.
- The user doesn’t want the manufacturer to link its ENS to its device public key.
The linkable signature solves the problem. The manufacturer checks the user’s claim to make sure that the current airdrop hasn’t been signed twice by the user i by calling the LINK function. The user’s identity remains anonymous.
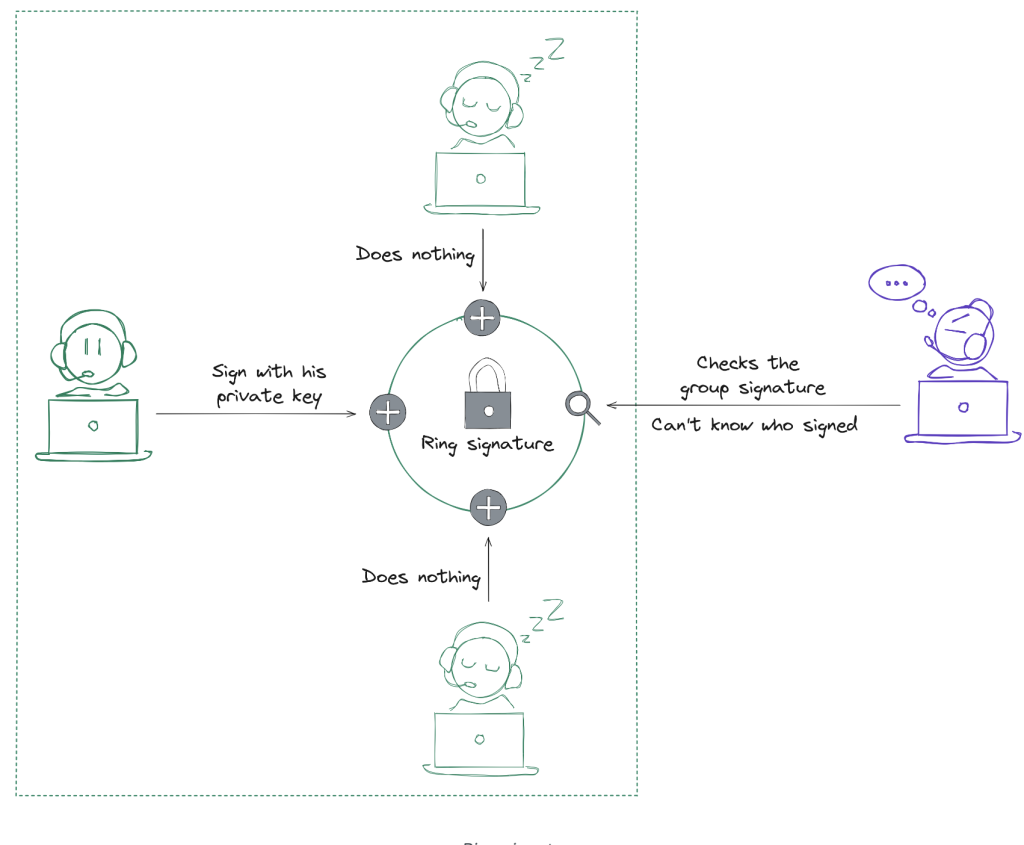
Here is what an airdrop using linkable signature looks like:
Airdrop use case
As you can see in the above example, thanks to the linkable property of the ring signature, the manufacturer providing the airdrop can make sure that nobody is able to claim the airdrop twice, without actually even knowing who claimed the airdrop.
These are just examples. Linkable signatures are a building block for the latest and most optimized versions of Confidential Transactions. These constructions enable confidential transactions (anonymization of a transactional system) like Zcash, Monero, or Tornado Cash.
Constructions allowing real privacy in transactions, such as Monero’s RingCT (Ring Confidential Transactions) and Triptych are built from a complex combination of three ZKP (Zero-Knowledge Proof) building blocks:
- Range proof,
- Commitment scheme,
- Linkable signature.
The combination and development of all those privacy-enhancing technologies might be the solution to build the strongest and safest privacy features through real-world use cases in the near future.
Imagine being able to prove your age or citizenship, but without having to give away all your passport information. Same thing when you want to get a loan from the bank, or when you’re looking for a flat in Paris. Doesn’t that bother you when you have to send a tax notification or a paycheck to a stranger only to prove that you have enough income? This could even change the way we vote. Imagine being able to vote from home, with the absolute certainty that there is no way to cheat and full privacy for everyone? Nobody can bribe lines of code.
This is just a glance at what ZKP (Zero-Knowledge-Proof) technologies could be in the future. Don’t you find that exciting?
Challenges Are Ahead
In order to efficiently use these technologies and apply them to real-world use cases at a bigger scale, we still need to improve them.
The main challenge for those efficient signatures is to maintain a reasonable complexity (in terms of signature size or signer and verifier computations), independently of the ring size (number of users in a ring).
Little overview of the tech side
Some improvements were already made, for instance by Monero. From their first version of Ring Signature (RingCT1) to the one today (Triptych / RingCT3), there is already a huge difference. In terms of computational cost, it went from a linear to a logarithmic curve, with good practical complexity improvements (factor 50 in size and 2 in speed). However, this computational cost is still a huge limit to the ring size. For a typical ring size of 2^10 users, the computational time is still 5 seconds on a PC, with a 10KB signature size.
The computational cost is still too expensive for constrained embedded devices such as the secure element on your Ledger Nano device, whose power and storage are way lower than a PC.
Since we believe in the importance of privacy, and that there are really interesting use cases, the optimization of those primitives (at the implementations and protocols level) is an ongoing research topic at Ledger.
Our Commitment To Privacy
As you may know, privacy is a major concern at Ledger. Privacy should never be taken for granted. For many years now, the digital field does not safeguard your privacy. Web2 companies are “free” platforms because you are the product. They collect, use, and sell your personal data, without you having any control over your digital life.
That’s why we, at Ledger, provide best-in-class self-custody solutions. Self-custody means true self-sovereignty when managing your digital assets interacting with your data. Like we already stated before, our incentives are not your data. We don’t make any money out of your data. We don’t even know who you are since we don’t hold your name and IP address.
While Tornado Cash being used by hackers has been legitimately sanctioned for money laundering concerns, we believe that the technology in itself shouldn’t be banned.
Open-source and privacy are not a crime. Zero-Knowledge-Proof (ZKP) technologies used by Tornado Cash, including Linkable Ring Signatures, are key foundations for the future of privacy and should not be discredited. They are solutions to privacy issues of the digital world. Let’s fight for them.