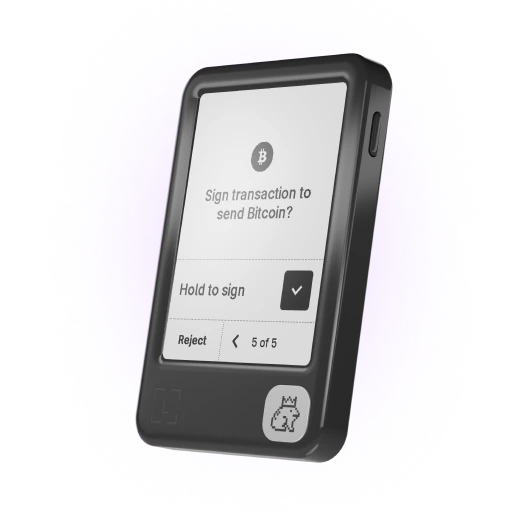
Compare Ledger signers
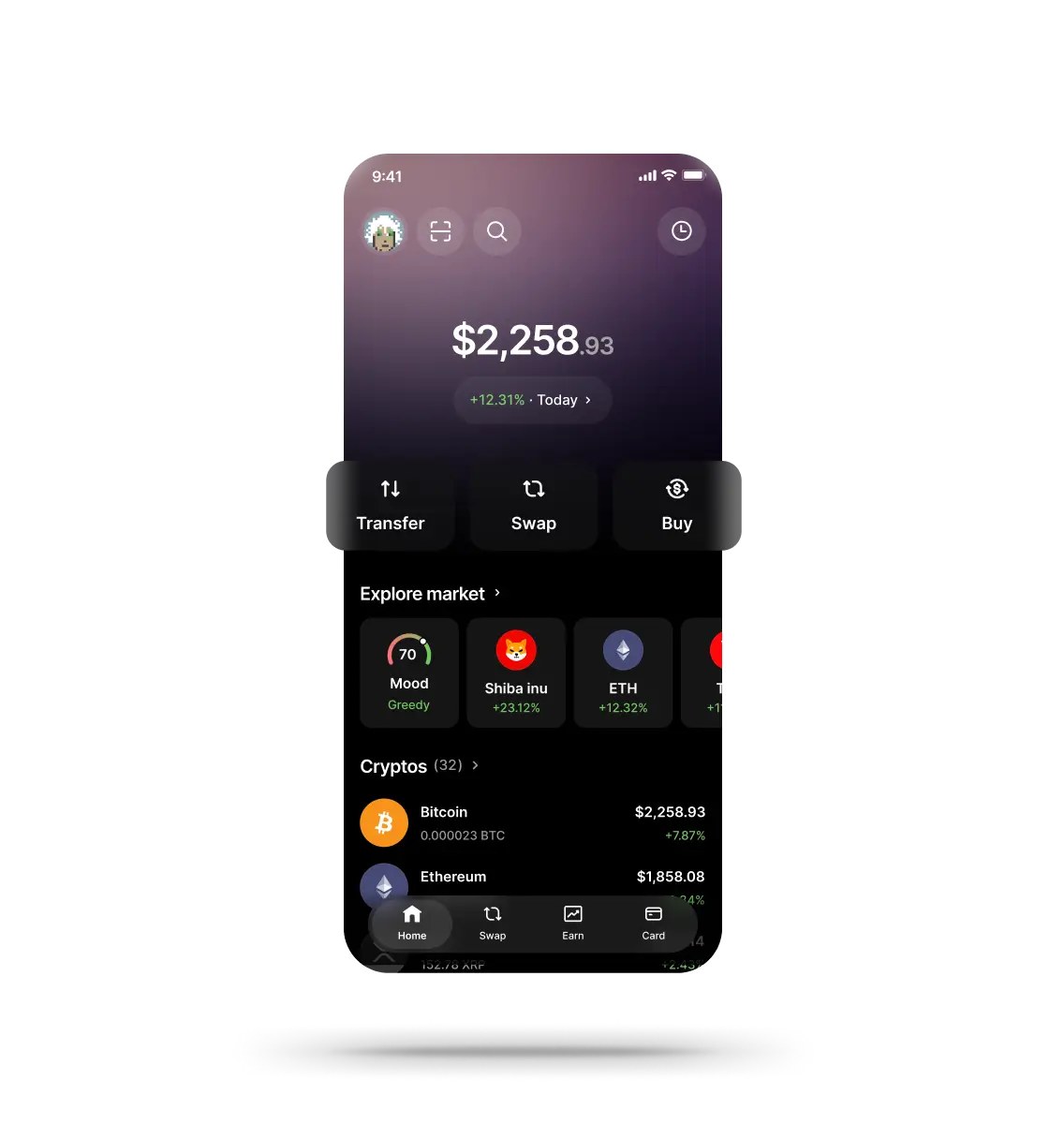
Ledger Signers & Crypto Wallets
Go beyond exchanges and software wallets
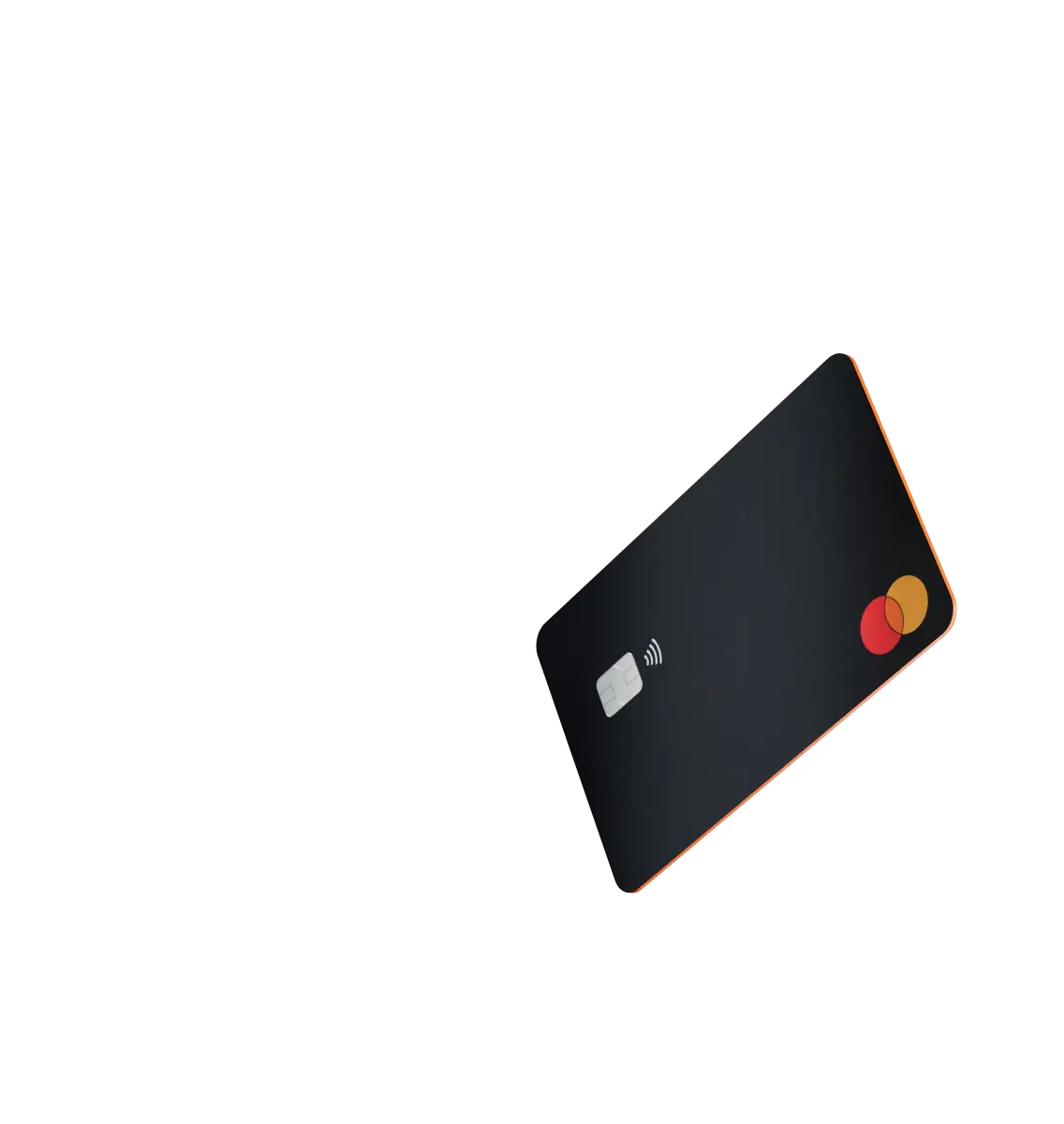
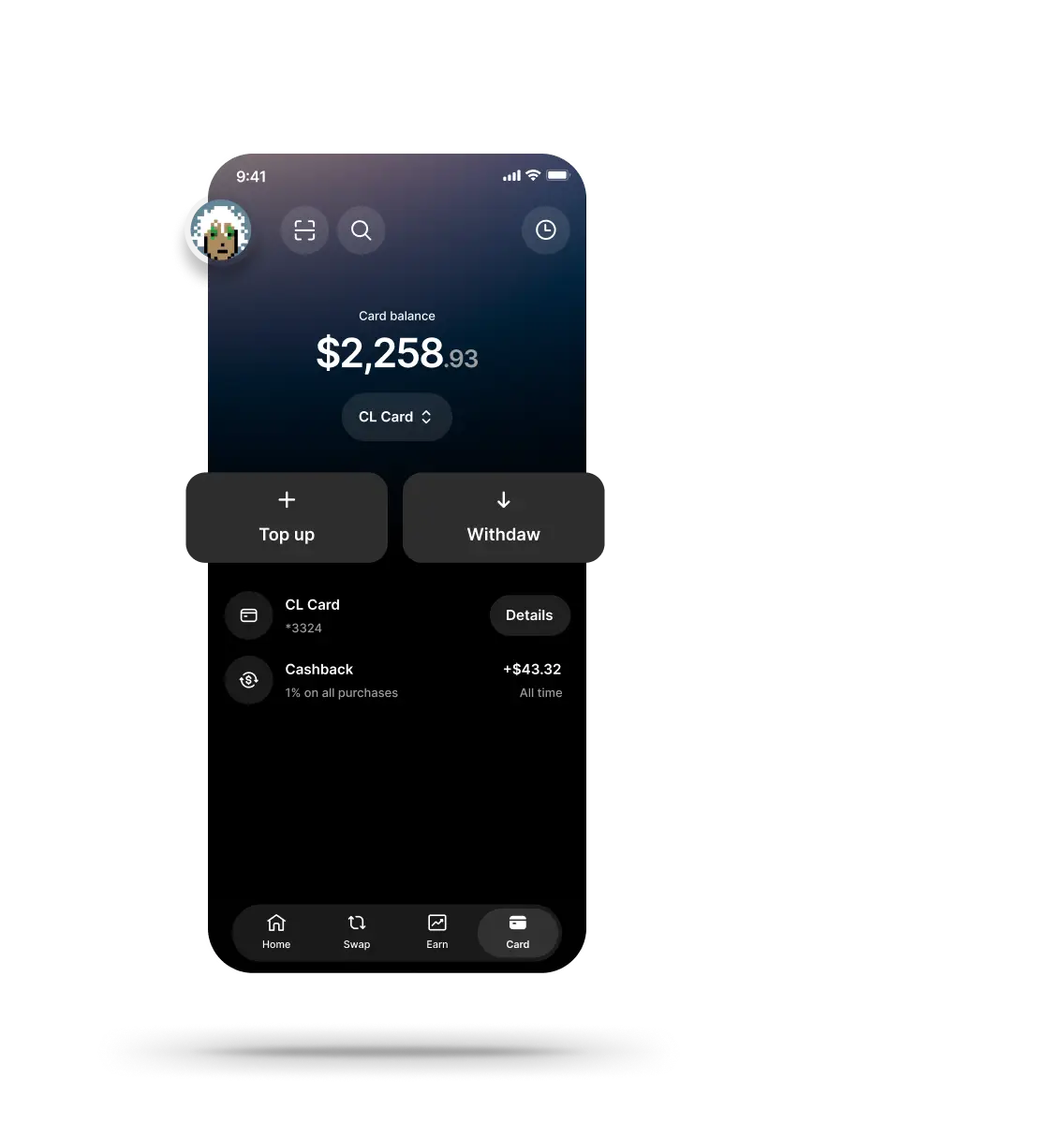
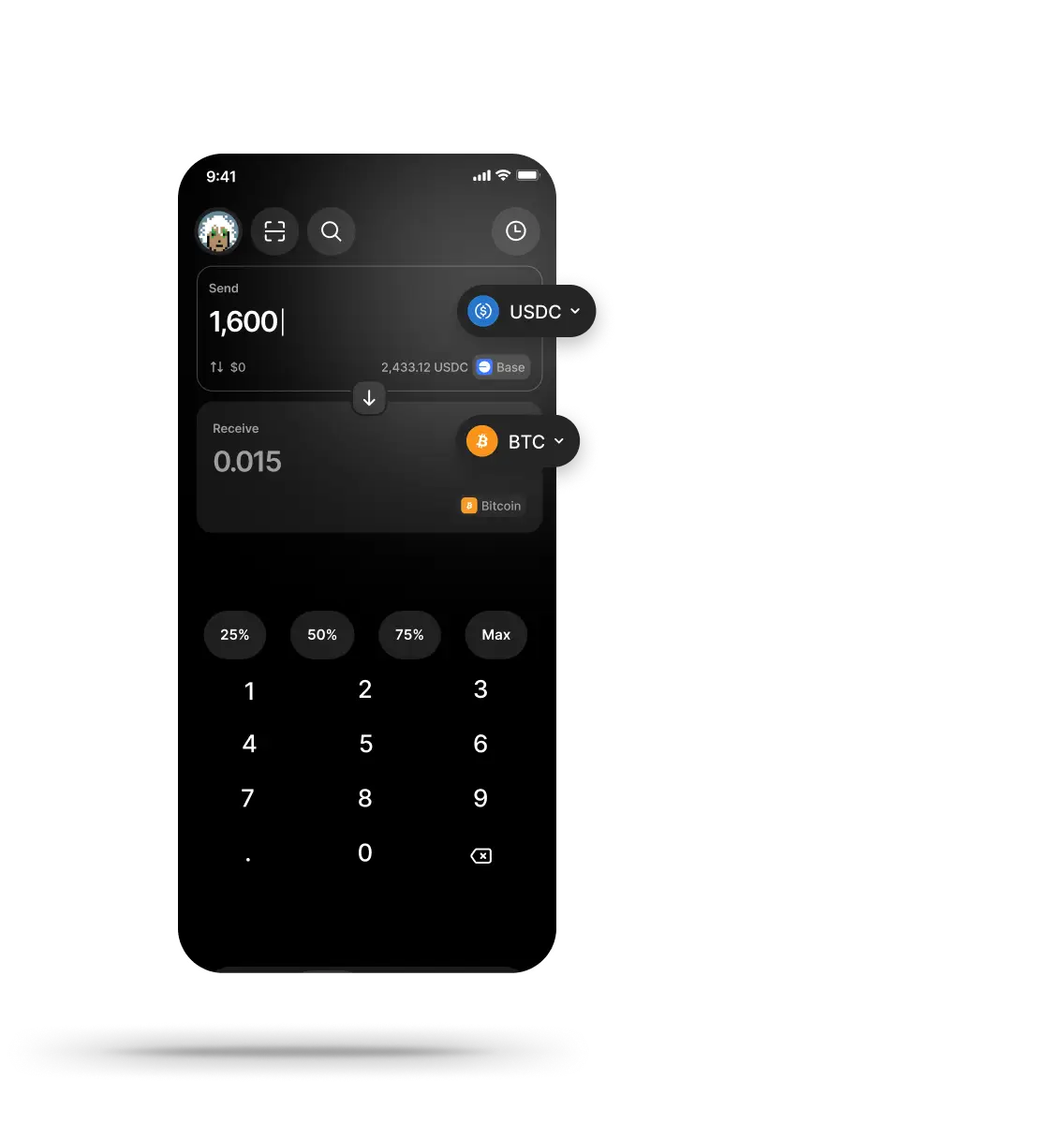
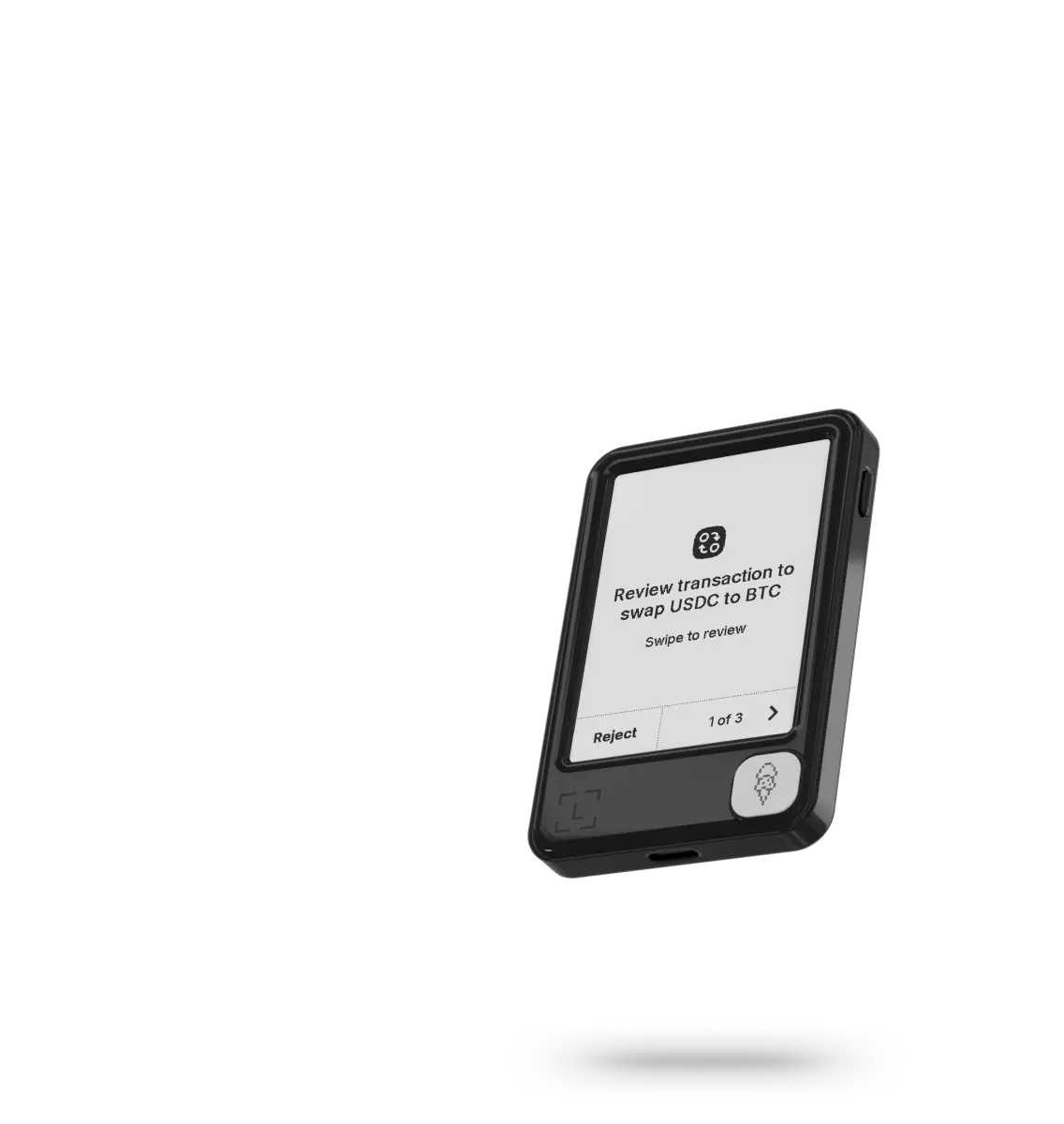
Meet the all new Ledger Wallet™ 4.0 to buy swap, stake and build easier than ever
-
20%+ global crypto secured
-
8+ million signers sold
-
Zero hacks