Donjon | 04/25/2026
Inside the Ledger Donjon: How a White-Hat Hacker Lab Works
Digital security is only as effective as the tools developed to test it. Explore the specialized hardware and open-source libraries used by the Ledger Donjon to fortify the global crypto industry through the principles of open security and responsible disclosure.
Before You Dive In:
- Effective security relies on the continuous development of specialized tools to simulate sophisticated attacks at the circuit and software levels.
- Open security is one of the Donjon’s core philosophies, meaning that the lab routinely releases its own internal methodologies and libraries to the global research community.
- Responsible disclosure ensures that vulnerabilities discovered in external products can be addressed through coordinated firmware updates before malicious actors can exploit them.
Previous installments of the Ledger Donjon series focused on the origin story of this unique white hat hacking lab and the importance of constant testing. However, the true strength of an attack-oriented lab is found in its arsenal.
To maintain an edge over malicious actors, the Ledger Donjon operates as a world-class research facility, building custom hardware and software to probe the deepest layers of both digital and physical security.
The Method of Attack: From Code to Circuit
A proper security evaluation requires consideration of all layers of a system, from the abstraction of software code to the granular reality of physical silicon. By considering the entire stack, the Donjon identifies potential vulnerabilities inside and across these layers, ensuring that defenses are multi-layered and resilient.
Side-Channel Resilience Through Simulated Attacks
At the software evaluation level, the objective is to verify the robustness of the firmware against physical attacks before the code is deployed. This is achieved through high-fidelity emulation using Rainbow, a Unicorn-based emulator.
Rainbow is a defensive tool that allows researchers to simulate side-channel leakage and observe code behavior under fault injection. This technique allows the Donjon to ensure that no vulnerabilities of this type are present in the analyzed firmware.
Side-Channel Analysis
Once the logical flow is understood, the focus shifts to the bridge between digital instructions and physical execution. Even the most perfectly written cryptographic algorithm can leak information if the implementation lacks sufficient hardening at both the hardware and software levels. Targeting these vulnerabilities is precisely what side-channel attacks attempt to do.
Essentially, as a chip processes sensitive data, it emits subtle signals, such as changes in power consumption, heat fluctuations, or electromagnetic emanations. To manage the massive datasets generated from these signals, the Donjon developed Lascar, an open-source python3 Side Channel Attack library. Lascar provides the primitives for end-to-end Side-Channel Analysis (SCA), including trace synchronization and leakage characterization.

Electromagnetic Fault Injection
Beyond passive monitoring, the Donjon also employs active disruption techniques. Fault injection involves perturbing a chip during critical operations to induce specific, exploitable errors.
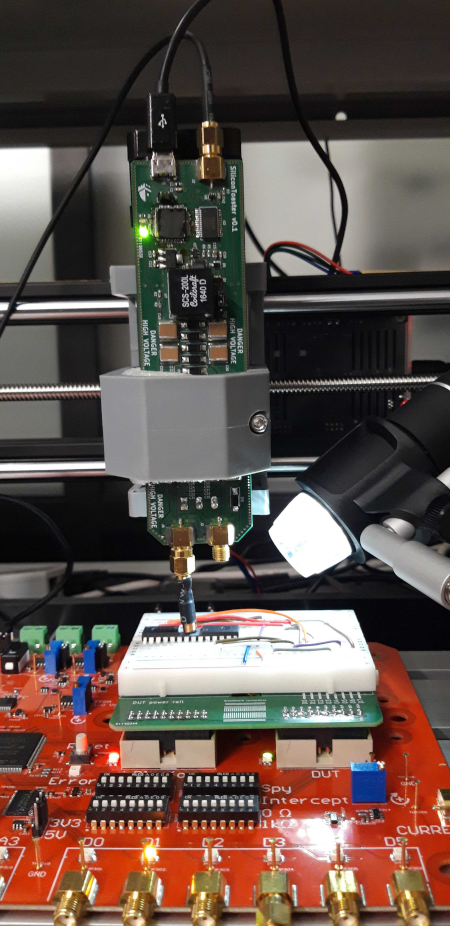
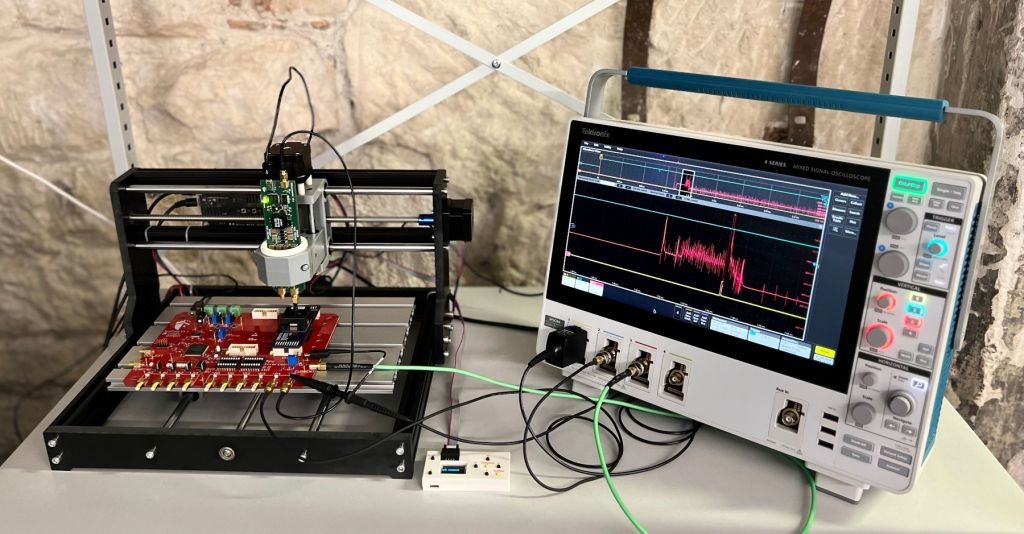
The primary tool for this technique is SiliconToaster, a custom-built Electromagnetic Fault Injection (EMFI) tool. SiliconToaster is capable of injecting high-voltage pulses of up to 1kV directly into the circuitry.
By carefully timing these pulses, researchers can confuse the chip into skipping a security check or bypassing a PIN delay. This technique simulates the high-level physical interventions available to many potential actors, due to its low cost and how easy it is to carry out. This technique was employed as part of the Donjon’s recent investigation into smartphone security, testing smartphone chips for vulnerabilities.
Laser Fault Injection
LFI is one of the key physical attack techniques that the Donjon uses in its testing. In this process, the team uses an oscilloscope to identify an appropriate timing window before using a microscope and laser to target specific regions of the chip.
The attack is performed in an exploratory way, scanning different areas until an unexpected behavior is observed, which helps the Donjon assess how the hardware responds to targeted fault injection during operations critical to security.
Beyond the Lab: Open Security & Coordinated Response
The findings produced during a security evaluation are not confined to the laboratory. To elevate security standards across the entire crypto space, Ledger transforms these internal insights into public-facing tools and coordinated security initiatives. This transition from laboratory testing to industry collaboration is a core pillar of the Donjon mission.
The Philosophy of Open Security
Ledger operates on the principle that security should not rely on obscurity. Instead, the Donjon promotes open security by sharing the knowledge and tools required to verify its findings. By open-sourcing libraries like Lascar and Rainbow, Ledger enables the global research community to build upon its work and ensures that scientific security research remains reproducible. This transparency extends to education through periodic Capture The Flag (CTF) challenges, which educate the community on complex bugs such as EOSIO VM memory access issues or Multi-Party Computation (SMPC) signature flaws.
Responsible Disclosure in Action
When researchers identify vulnerabilities in third-party hardware or software, they follow a strict protocol of responsible disclosure. This ethical framework ensures that a manufacturer is notified of a flaw and given an appropriate window to develop and release a patch before the findings are made public. Public disclosure remains a necessary step so that users are informed of the vulnerabilities, especially if those vulnerabilities can only be mitigated and not fully patched.
By working with the broader industry, the Donjon ensures that the entire crypto ecosystem becomes more resilient. This effort is complemented by the Ledger Bug Bounty program, which invites the global community to stress-test the Ledger ecosystem alongside the lab’s internal experts.
The Ledger Ecosystem: Secure Digital Ownership
The sophisticated tech stack and rigorous methodologies of the Donjon are not merely academic exercises; they are the foundation of the Ledger ecosystem. The synergy between Ledger Wallet and Ledger signers is maintained through this constant process of breaking and building.
Every tool created in the lab, from Lascar to SiliconToaster, serves to harden the boundary between a user’s assets and the myriad threats of the digital age. This commitment to verified technical evidence ensures that digital sovereignty remains a reality for every Ledger user. Security is the foundation upon which the entire ecosystem is built, ensuring that the digital future remains exclusively in the hands of the user.
Ready to see the hackers in action? Watch the YouTube series, Enter the Donjon, to go behind the scenes. See the lasers, the glitches, and the elite research that keep your digital assets safe from the threats of today and tomorrow.
































