Donjon | 04/29/2026
The Hidden Risk of Side-Channel Attacks on Post Quantum Cryptography
While the standards for Post-Quantum Cryptography have arrived, quantum-safe math is only half the story. This article explores how physical chips can still leak your secrets, and the hardware security needed to protect them.
Before You Dive In:
- Quantum-safe algorithms like ML-KEM are mathematically sound, but a device running unprotected code can still leak secret key material through its electromagnetic emissions and power consumption, a technique known as a Side-Channel Attacks (SCAs).
- The Donjon team shows practically that PQC open source implementations such as PQM4 can be attacked easily after collecting only 40 EM traces within a minute.
- Hardware-level countermeasures like masking, shuffling, and desynchronization are essential because a cryptographic vault is only as strong as the physical walls built around it.
- This article continues the Ledger Donjon’s focus on post quantum cryptography, which began by looking at the potential implications of PQC’s threat to blockchain and the enduring needs for secure keys.
The cryptography world recently crossed a massive milestone. To protect our digital infrastructure from the looming threat of quantum computers, NIST finalized its standards for Post-Quantum Cryptography (PQC). The undisputed stars of this new era are the CRYSTALS algorithms: Kyber (now officially ML-KEM for key encapsulation) and Dilithium (now ML-DSA for digital signatures).
Mathematically, these lattice-based algorithms are built on solid foundations. They are designed to withstand attacks from both classical supercomputers and future quantum machines. But there is a plot twist: while the math is rock-solid, the physical devices running that math might be spilling secrets.
Welcome to the stealthy world of Side-Channel Attacks (SCAs). Here is why the next big challenge in the quantum transition isn’t about fixing the algorithms—it’s about securing their implementations.
What is a Side-Channel Attack?
Imagine a master safe-cracker. Instead of trying to guess the million possible combinations to a vault (a brute-force attack) or trying to melt the door (a mathematical break), the thief simply places a stethoscope against the metal and listens. By listening to the faint “clicks” of the gears, the thief figures out the combination.

Side-channel attacks work exactly the same way, but on microchips.
When a processor executes a cryptographic algorithm like CRYSTALS-Kyber, it consumes power and emits faint electromagnetic (EM) signals. A hacker with physical proximity can measure these physical “exhaust fumes”. By analyzing such leakage during the algorithm execution, an attacker can infer the secret key without ever breaking the underlying math. Several practical examples have been shown in the literature, such as [1, 2, 3].
ML-KEM
ML-KEM stands for Module-Lattice-based Key-Encapsulation Mechanism. While that sounds like a mouthful, it describes a fundamental shift in how we protect data.
Before its standardization, it was known as CRYSTALS-Kyber. It belongs to a family of “Post-Quantum Cryptography” (PQC) algorithms designed to be secure even if an adversary has a cryptographically relevant quantum computer (CRQC) capable of running Shor’s algorithm.
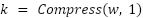
It is a Key Encapsulation Mechanism: rather than performing a Diffie-Hellman-style key agreement, one party generates a fresh random secret and transmits it to the other party in encrypted form. The recipient decrypts it. Both ends then hold the same secret, which can be used as the key for a symmetric cipher for the actual session.
The three operations are:
- Key Generation (KeyGen): Generates an asymmetric key pair. The encapsulation key (public key) is distributed. The decapsulation key (private key) is kept secret by its owner.
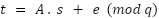
where t and A are the public keys, s and e are secrets.
- Encapsulation (Encaps): Takes the recipient’s encapsulation key, generates a fresh random shared secret (k), encrypts it into a ciphertext. Then, the ciphertext is sent to the recipient.
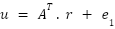
where is random, 1 and 2 are error vectors, and are the ciphertext.
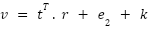
- Decapsulation (Decaps): Takes the ciphertext and the decapsulation key , and recovers the same shared secret that was generated during encapsulation.
where is the noisy message .
ML-KEM is available in three different security levels:
| Variant | Module Rank (k) | Security Level |
| ML-KEM-512 | 2 | NIST Level 1 (AES-128) |
| ML-KEM-768 | 3 | NIST Level 3 (AES-192) |
| ML-KEM-1024 | 4 | NIST Level 5 (AES-256) |
Open Source Implementations
Integrating ML-KEM into embedded systems is a high-stakes engineering task where memory safety and timing-predictability are paramount. The constraints shift from raw throughput to memory footprint (RAM), code size (Flash), and power consumption. Since ML-KEM uses lattice-based math involving Polynomial Multiplication (NTT), implementations for microcontrollers often require specific optimizations for ARM Cortex-M or RISC-V architectures.
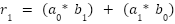
One of these implementations is pqm4, which is a definitive benchmarking framework and library for the ARM Cortex-M4. It is widely utilized because it includes hand-optimized assembly for the Number Theoretic Transform (NTT), leveraging the M4’s SIMD (Single Instruction, Multiple Data) instructions.
The evaluation of the hardware security of PQM4 implementation on the STM32-F4 (running at 84 MHz) was the primary focus of this work.
Evaluation Against Side-Channel Attacks
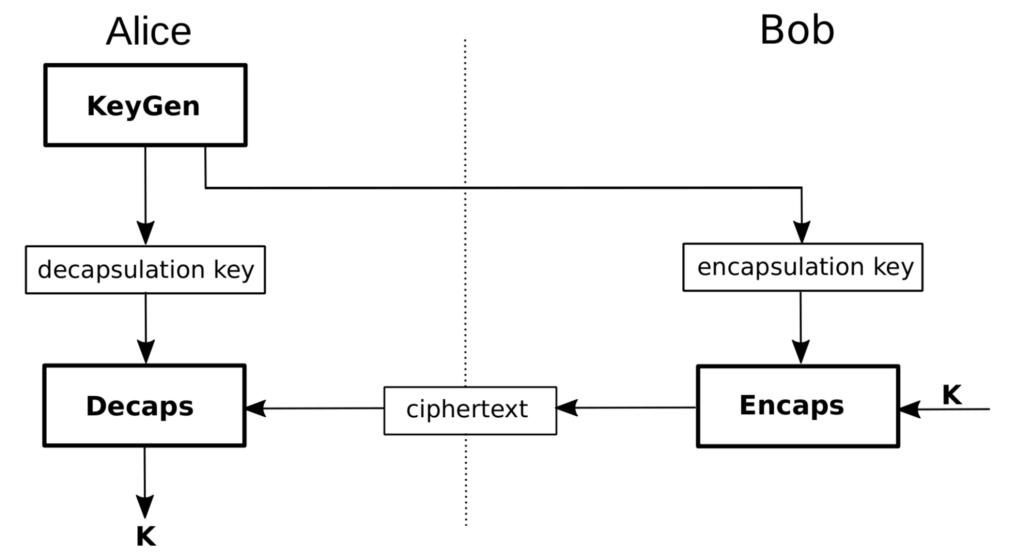
We focused on the decryption process where the secret key is (sk) manipulated by the function poly_frombytes_mul. The goal is to assess whether this key can be attacked using side-channel attacks, given the attacker has physical access to the target and can challenge the algorithm with controlled ciphertexts without knowing the key.
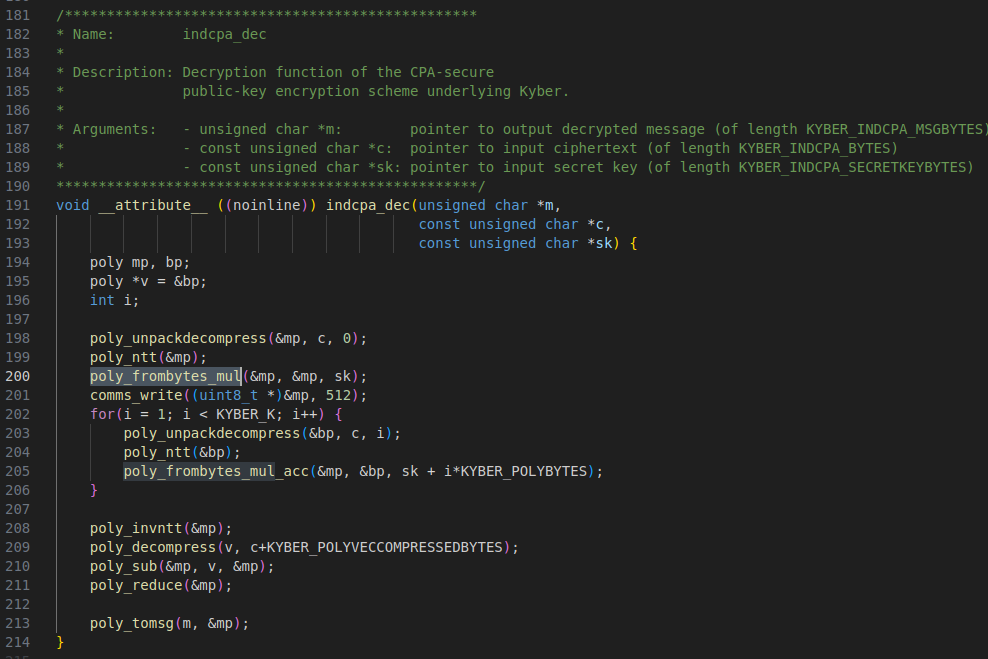
The experimental setup, depicted below, was constructed to capture electromagnetic (EM) signals emanating from the development board during the decryption process. Key components include a high-end oscilloscope with a sampling rate up to 6.25 Gs/second, an EM probe, and an amplifier used to boost the signal from the probe. The evaluation target executing ML-KEM is the STM32F4 microcontroller.
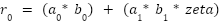
Monitoring of the Electromagnetic (EM) signal was initiated during the execution of the assembly-optimized function, poly_frombytes_mul, on the chip. This function, which is entirely written in assembly for performance optimization, processes two inputs: a, the secret key in NTT format, and b, the public ciphertext, and outputs r. The operation is represented by the following equations:
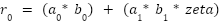
where zeta is a constant related to NTT calculation.
Our experiment focused on a side-channel attack using Correlation Power Analysis (CPA) to uncover secret keys. This statistical technique breaks encryption by monitoring the electromagnetic (EM) emissions of a processor during operation. Unlike conventional cryptanalysis, CPA treats the encryption algorithm as a physical process.
The procedure involved collecting EM traces while systematically varying the ciphertext (ct), keeping the secret key constant. The core principle of CPA relies on the relationship between a device’s power consumption and the Hamming Weight (number of ‘1’ bits) of the data being processed.
By capturing thousands of power or EM traces and correlating them with a mathematical model using the Pearson correlation coefficient, an attacker can test hypotheses for parts of the secret key. A successful key guess is indicated by a high correlation peak against the actual measured power, thereby revealing a segment of the secret key.
This method goes beyond simple observation of power “spikes”; it employs the Pearson Correlation Coefficient to statistically establish a link between a mathematical model of the power consumption and the actual physical measurements.
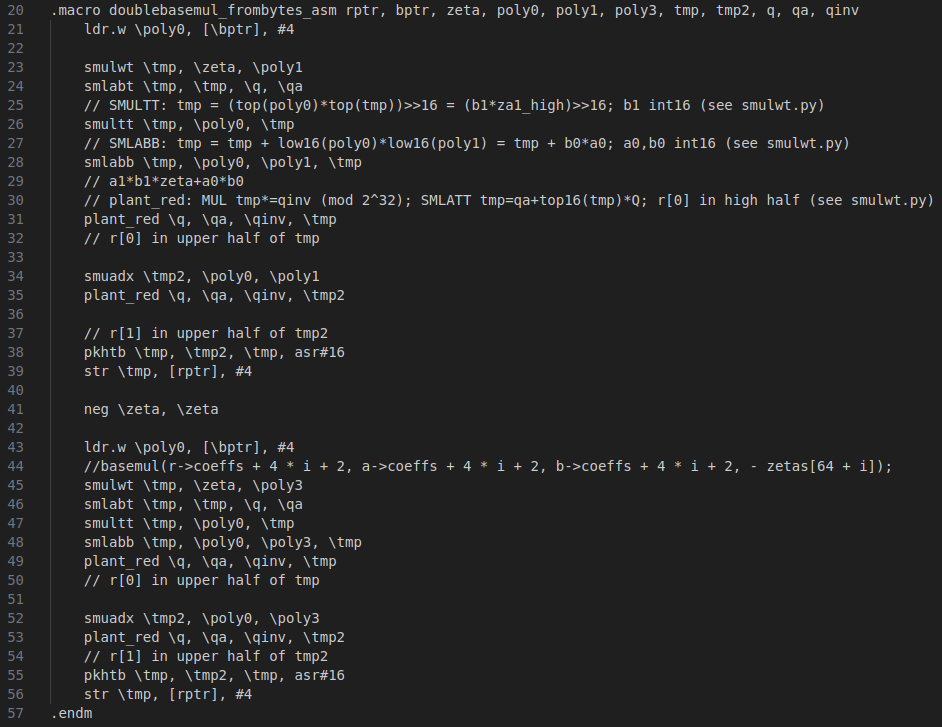
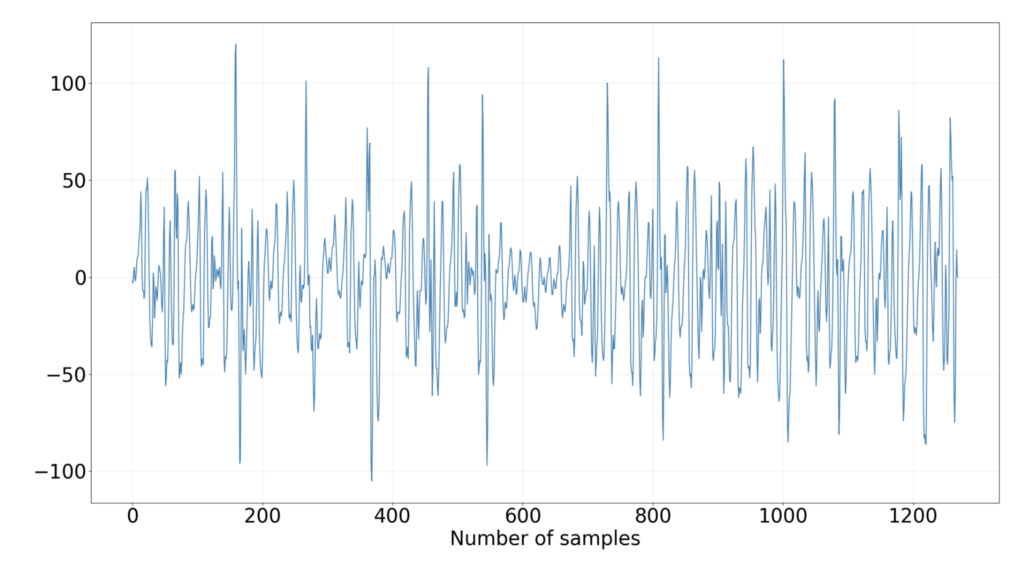
The figure presented below displays an Electromagnetic (EM) trace recorded during the execution of the poly_frombytes_mul function. This is followed by a second figure that specifically highlights the initial activity of poly_frombytes_mul, which corresponds to the processing of the first two secret values, 0 and 1.
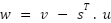
The attack focuses on the equation
By carefully selecting a ciphertext, we can generate two distinct datasets. In the first dataset, 0 is set to facilitate the attack on 1. Conversely, in the second dataset, 1 is set to target 0. This approach primarily aims to circumvent the difficulty of a combined two-byte CPA attack, as it reduces the guess space significantly from 24 to 12.
Note: 0 and 1 are vectors of 12-bits. This is referred to as a selective-based ciphertext attack.
As an example, for attacking 1, the leakage model will be like what is shown below, where guess is the guessed key 1, which ranges from 0 to 3329 (modulo ). The same is done for attacking 0.
For instance, to target 1, the leakage model will be configured as shown below. The guess parameter represents the hypothesized key 1, which falls within the range of 0 to 3329 (modulo ). A corresponding process is applied when targeting 0.
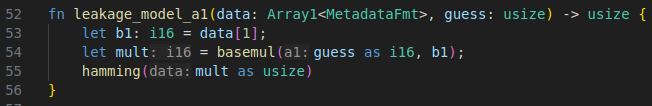
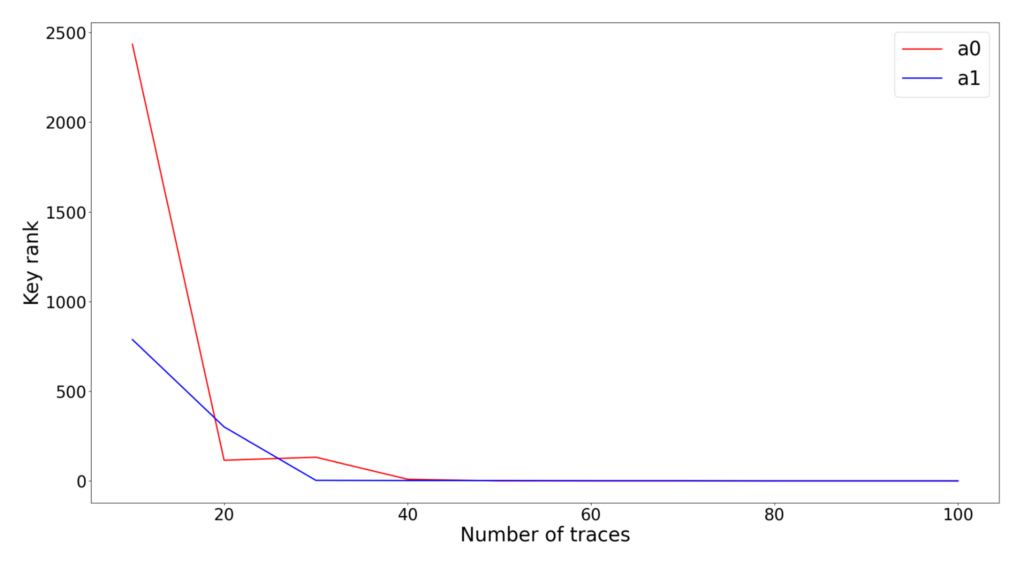
The attacks on 0 and 1 have been completed, and the results from the CPA are illustrated in the following two visualizations below. We show the correlation of all 3329 ( to q-1) guessed values over the time samples. In both scenarios, the correct key values demonstrate the highest correlation, which is evident from the plots.
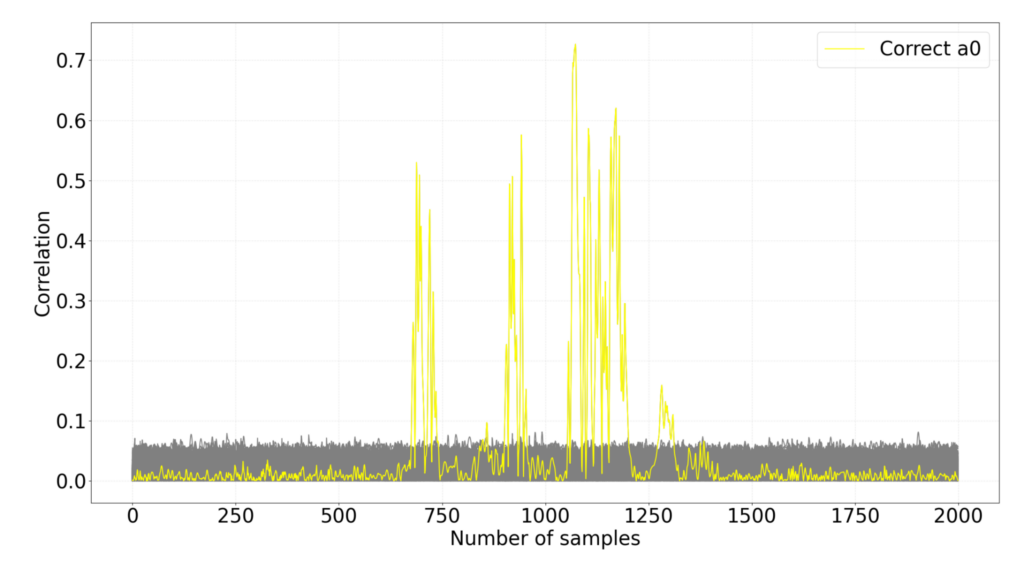
A key success metric is the number of electromagnetic (EM) traces required to achieve a successful key rank. For both cases, approximately 40 EM traces were needed for a successful attack, a collection process that takes less than a minute.
The Real-World Risk
You might be thinking: “An attacker needs physical access to measure power? That doesn’t sound like a major threat.”
Unfortunately, it is. Think about hardware wallets, smart cards, IoT devices, USB security keys, and mobile phones. If you lose your security key, a malicious actor can take it to a lab, hook it up to an oscilloscope, and extract your PQC private keys within minutes if the chip isn’t protected.
Building the Shield: Countermeasures
To safely deploy such algorithms in the real world, engineers cannot just copy and paste the mathematical formulas into code. They have to build defensive walls.
1. Masking (The primary defense): Masking splits a secret key into multiple random “shares” before processing it. The processor never computes the full secret all at once, so the power consumption at any given millisecond only reflects random noise, confusing the attacker.
2. Shuffling: Instead of processing data in a predictable, linear order (Step 1, Step 2, Step 3), the algorithm randomizes the order of independent operations. This will force the attacker to acquire more traces for a successful attack.
3. Desynchronization: While shuffling randomizes the order of operations, desynchronization focuses on randomizing the timing by adding random delays during the execution. As a result, the attacker should perform sophisticated signal processing to align the traces carefully.
The Takeaway
The transition to Post-Quantum Cryptography is not just a software update; it is a fundamental hardware and implementation overhaul. Algorithms such as ML-KEM will secure the internet for the next century, but only if we remember that a cryptographic vault is only as strong as the physical walls built around it. As organizations begin migrating to PQC, asking “Is it quantum-safe?” is no longer enough. The real question is: “Is it side-channel safe?”.
Karim M. Abdellatif, Ph.D. & Alain Magazin
Security Engineers
































